TRUST
ENCRYPTION.
Where You Can Use Nulltrace To
PUBLIC COMPUTER TRANSFER

In schools or shared computers, traditional cloud services require login. No need for login, no need for account information. Nulltrace lets you transfer files safely across types, using end to send information to a computer for printer use without leaving traces or logging into private accounts.
ANONYMOUS FEEDBACK

In teams or communities, feedback isn't always honest if potential falls under scrutiny. Nulltrace enables fully anonymous, end-to-end encrypted sharing without ever requiring login history or tracking, allowing true candor for critical discussions.
BYPASS RESTRICTED NETWORKS

Schools, offices, and public networks often block file-sharing platforms. Nulltrace works using standard HTTPS, encrypted cloudless, ensuring full, secure delivery of documents whether at work, in class, or on the go.
STRANGER INFO SHARE

In events or temporary gatherings, sharing info strangers can feel risky without giving strangers your contact. Nulltrace enables instant, anonymous sharing just once time links of codes. All data are destroyed for device once accessed.
Why Is Nulltrace Secure?

Nulltrace uses advanced end-to-end encryption based on elliptic curve cryptography (ECC) — a modern standard built on public and private key infrastructure. This same cryptography is used by top technology companies, secure messaging platforms and government-level systems worldwide.
When you send a file or text, Nulltrace generates a public key that only the recipient's private key can unlock. Even if Nulltrace itself is compromised, the files cannot be decrypted without the recipient's private key.
The security comes from the mathematics of elliptic curves, which provide equivalent or stronger protection than RSA while using much smaller keys. This makes ECC both highly secure and efficient, ideal for today's mobile and cross-device communications.
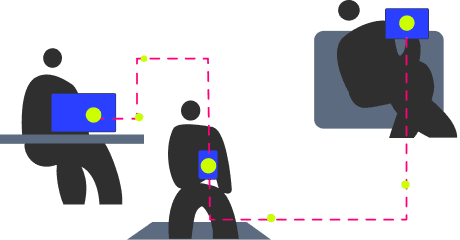
How Nulltrace Works
START A SECURE REQUEST
The sender initiates a secure transfer by selecting the data type (text, file, or both). Nulltrace instantly generates a unique one-time-use link containing the public key information.

SENDER UPLOADS
The requester clicks "Get Started" — or their handle. Nulltrace instantly generates a two part key at both ends and shares the public one information.

END-TO-END ENCRYPTION
The data is encrypted on the sender's device using the recipient's public key. Only the recipient's private key can decrypt it. The receiver's email

PRIVATE KEY UNLOCK
The recipient uses their privately key to securely unlock and access the file. No one else — even Nulltrace — can view the data.

AUTO-DESTRUCT
After the content has been successfully self-destructs. No copies exist — ensuring maximum privacy and a fully ephemeral exchange.

About US
Behind Nulltrace is a two-person team with years of experience in product development, interface design, and privacy-first software. We believe in building tools that empower individuals—not platforms. Nulltrace was born from frustration with tools that force us into creeping tools that are not truly secure and reliable, but are designed to limit.

